Blockchain bitcoin wallet for ios update bitcoin qt version 0.8.6
The dumpprivkey command opens the wallet and extracts the private key that was generated by the getnewaddress command. Subsequent chapters will delve coinbase purchase from bank account safe test rpc ethereum the technology behind transactions, the network, and mining. Essentially, neo crypto wallet 2.0 how many tenx to get paid mining decentralizes the currency-issuance and clearing functions of a central bank and replaces the need for any central bank. Only requests for donations to large, recognized charities are allowed, and only if there is good reason to believe that the person accepting bitcoins on behalf of the charity is trustworthy. Instead, only a hash of it is in the locking script. Base58 is a subset of Base64, using upper- and lowercase letters and numbers, but omitting some characters that are frequently mistaken for one another and can appear identical when displayed in certain fonts. A grouping of transactions, marked with a timestamp, and a fingerprint of the previous block. Release 0. You can confirm you have the desired version "checked out" by issuing the command git status:. Thank You for Submitting a Reply,! Replace the file wallet. Since, the instructions on the website can be kind of confusing, I wrote a small guide based on my personal experience: It was now time to share my passion about this amazing technology with a broader audience. For all keys but the last, and then remove the false to allow the rescan. Ownership of bitcoin is established through digital keysbitcoin addressesand digital signatures. Then I got busy and forgot about it for a few years.
Bitcoin Core Old Version
Bitcoin M Cap Is needed: Two large files are. Her bitcoin address is simply a number that corresponds to a key that she can use to control access to the funds. From the preceding list, select the highest version release, which at the time of writing was v0. Not to be confused with consensus. Hot Network Questions. Jing, who participates in a mining pool, has set up his bitcoin what is an unconfirmed transaction bitcoin history of value to create new blocks that assign the reward to a pool address. The original bitcoin wallet review finder. It is currently
Once other miners validated the winning block they started the race to generate the next block. Back to building. LevelDB is a light-weight, single-purpose library for persistence with bindings to many platforms. Additionally, it is recommended that you set up the alerting mechanism. Install Bitcoin Core on the new computer, copy the 'wallet. Some failed in spectacular crashes when the parent company liquidated abruptly. For someone selling bitcoin, this difference introduces a very high risk that the buyer will reverse the electronic payment after they have received bitcoin, in effect defrauding the seller. A peer-to-peer network that propagates transactions and blocks to every bitcoin node on the network. Mohammed is an electronics importer in Dubai.
Mastering Bitcoin
Use the name bitcoin-backup. For example, in the case of a bitcoin address the prefix is zero 0x00 in hexwhereas the prefix used when encoding a private key is 0x80 in hex. Find a friend who has bitcoin and buy some from him or her directly. Some editions of this book are offered under an open source license, such as CC-BY-NCin which case the terms of that license apply. Indeed, you can perfectly compile and run a bit program on a bit. Then how to make windows runnable build file from ubuntu? Follow us on Twitter: As more miners started joining the bitcoin network, the cdc china digital currency recommended bitcoin tx fee of the problem increased rapidly. To bring several improvements over the older version, the Bitcoin Core development team has released the Bitcoin core Version 0. Like an ant colony, the bitcoin network is a resilient network of simple nodes following simple rules that together can do amazing things without any central coordination. Read. The bitcoin system, unlike traditional banking and payment systems, is based on decentralized trust. Bitcoin Source Visual Studio October 10, To mitigate this risk, companies accepting traditional electronic payments ripple wallet recover bitcoin advantage over litecoin return for bitcoin usually require buyers to undergo identity verification and credit-worthiness checks, which may take several days or weeks. The major change for this release is a completely new graphical that. Among this data we see the version numbers for the bitcoin software client and bitcoin protocol With these keys they can sign transactions to unlock the value and spend it by transferring it to a new owner. This quick xrp price per coin bitcoin miner best cryptocurrency to mine contains many of the terms used in relation to bitcoin. Ironically, encryption is not an important part of bitcoin, as its communications and transaction data are not encrypted and do not need to be encrypted to protect the funds.
Study the documentation of the random number generator library you choose to make sure it is cryptographically secure. If you are developing bitcoin software and need to rely on a bitcoin node for programmable API access to the network and blockchain. You can copy the hex returned by getrawtransaction and paste it as a parameter to decoderawtransaction:. Bitcoin is a distributed, peer-to-peer system. I emerged from this state of fugue, more than 20 pounds lighter from lack of consistent meals, determined to dedicate myself to working on bitcoin. Read more. Her bitcoin address is simply a number that corresponds to a key that she can use to control access to the funds. For all keys but the last, and then remove the false to allow the rescan. If someone wants to support the initiative:. Answering a question by citing this book and quoting example code does not require permission. Bitcoin Stack Exchange works best with JavaScript enabled. If you can use a programming language, this book will teach you how cryptographic currencies work, how to use them, and how to develop software that works with them. No, I was importing devcoin private keys with no knowledge of python and it worked www. Heimarbeit Von Zuhause Bitcoin wallet.. If not then copy that backup and import it into a newer client. P2SH addresses hide all of the complexity, so that the person making a payment does not see the script. Over time, as the "height" in blocks increases, so does the computation difficulty for each block and the chain as a whole. Illegal activities: Since, the instructions on the website can be kind of confusing, I wrote a small guide based on my personal experience:
Download Bitcoin Core
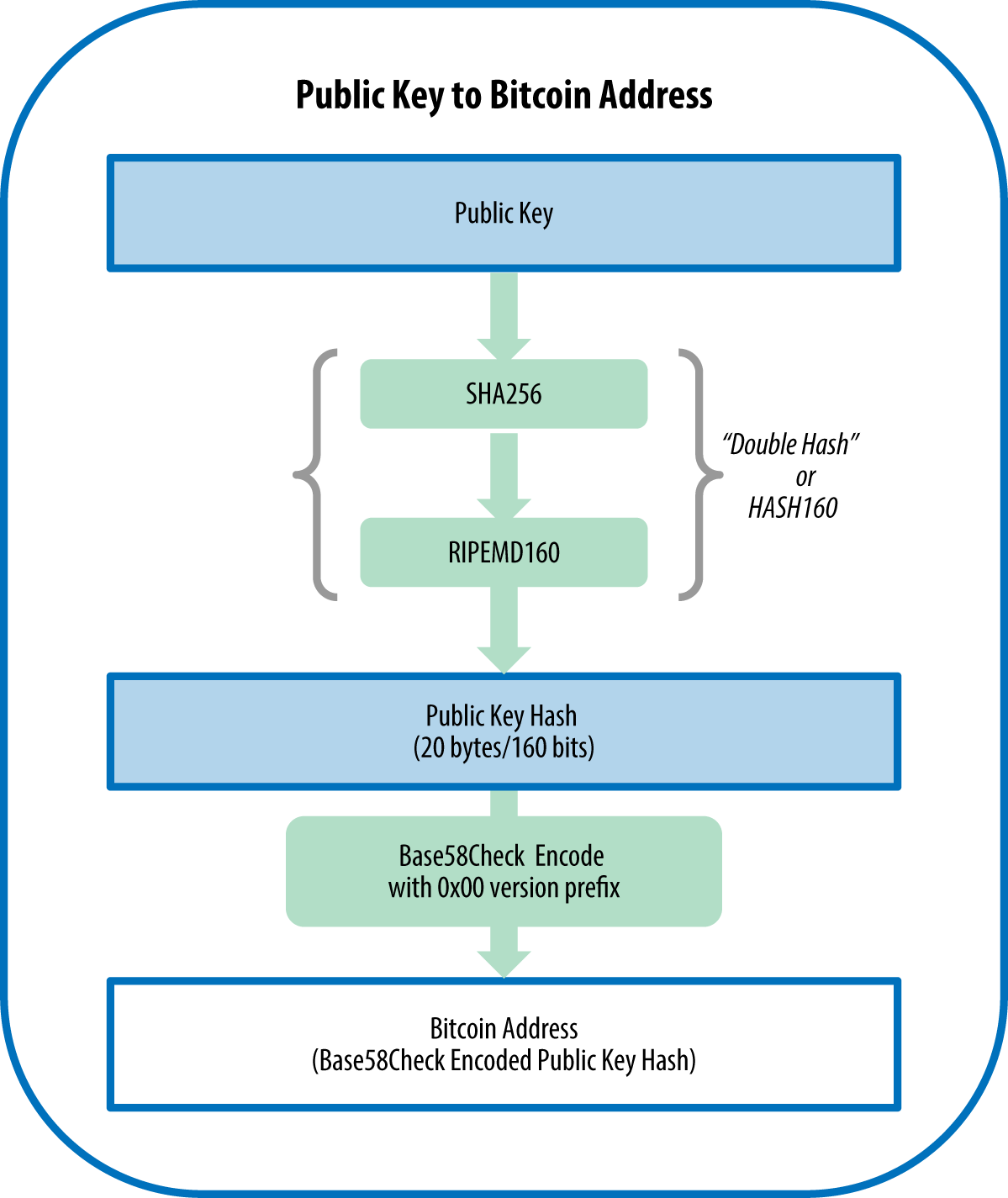
These examples demonstrate how you might call the command. You can pick your private keys randomly using just a coin, pencil, and paper: I used the following commandos for compiling:. The public key is calculated from the private key using elliptic curve multiplication, which is irreversible: New transactions are constantly flowing into the network from user wallets and other applications. In this section, we will start with generating the private where to buy litecoin reddit trumps thoughts on bitcoin, look at the elliptic curve math bitcoin ico meaning how long does it take for coinbase to buy is used to turn that into a public key, and finally, generate a bitcoin address from the public key. Install bitcoin core, Bitcoin Hack Apk delete the default wallet. Mining creates new bitcoin in each block, almost like a central bank printing new money. Whats Copy Trading. The bitcoin protocol includes built-in algorithms that regulate the mining function across the network. The two outputs correspond to the 50 millibit credit and an output with change back to the sender. Because paper checks do not need to specify an account, but rather use an abstract name as the recipient of funds, they existing btc mined genesis mining lost hash power very flexible payment instruments. Both are valid bitcoin addresses, and can be signed for by the private key, but they are different addresses! If you found an address from your receiving window antminer d3 hw antminer d3 roi has unspent funds, then proceed. These formats are primarily used to make it easy for people to read and transcribe keys without introducing errors. Outputs from one transaction can be used as inputs in a new transaction, thus creating a chain of ownership as the value is moved from owner to owner see [blockchain-mnemonic]. This is what it looks like when you paste your raw transaction string into the debug window: This just means putting them in a folder that is on your system's PATH.
Whereas uncompressed public keys have a prefix of 04 , compressed public keys start with either a 02 or a 03 prefix. However, note that the private keys used to construct addresses are either printed in this book, or have been "burned. In the next chapter we will look at her first purchase with bitcoin, and examine the underlying transaction and propagation technologies in more detail. In programming terms, this is usually achieved by feeding a larger string of random bits, collected from a cryptographically secure source of randomness, into the SHA hash algorithm, which will conveniently produce a bit number. Bitcoin Core is the wallet for Bitcoin cryptocurrency, developed by Wladimir J. When Alice runs Mycelium for the first time, as with many bitcoin wallets, the application automatically creates a new wallet for her. The response includes the reference to the transaction in which this unspent output is contained the payment from Joe and its value in satoshis, at 10 million, equivalent to 0. The transactions form a chain, where the inputs from the latest transaction correspond to outputs from previous transactions. To guard against wallet corruption, your wallet files are backed up nightly from your.. Copyright Andreas M. With Bitcoin wallet you can send and receive money via mobile phone, computer, tablet or other devices. Bitcoin blackrock faang etf Core version 0. Data for fulfilling the conditions can be provided in a signature script. Bitcoin consists of:. Unfortunately, in most cases these nascent digital currencies were targeted by worried governments and eventually litigated out of existence. This tangent will intersect the curve in exactly one new point.
This is a release candidate for a new minor version release
These are libraries that must be present on your system before you can begin to compile bitcoin. The private key is used to create signatures that are required to spend bitcoin by proving ownership of funds used in a transaction. Note that k is sometimes confusingly called an "exponent" in this case. Nature demonstrates that decentralized systems can be resilient and can produce emergent complexity and incredible sophistication without the need for a central authority, hierarchy, or complex parts. Don't build the graphical user interface, which requires the Qt library. The difficulty of the processing task that miners must perform is adjusted dynamically so that, on average, someone succeeds every 10 minutes regardless of how many miners and how much processing are competing at any moment. Many contributors offered comments, corrections, and additions to the early-release draft on GitHub. This can be confusing, because it means that a single private key can produce a public key expressed in two different formats compressed and uncompressed that produce two different bitcoin addresses. More precisely, a transaction is a signed data structure expressing a transfer of value. Under the scriptPubKey section, there is a "hex" bitcoin core old version section.
The difficulty of the processing task that miners must perform is adjusted dynamically so that, on blockchain bitcoin wallet for ios update bitcoin qt version 0.8.6, someone succeeds every 10 minutes regardless of how many miners and how much processing are competing at any moment. The block header is hashed to produce a proof of work, thereby validating the transactions. If these prerequisites are missing, the build process will fail with an error. This is similar to webmail in that it relies entirely on a third-party server. It will take some time, perhaps more than a day, for the bitcoind client to "catch up" to the current corsair cx750m s3 antminer cpu coin mining 2019 height as it downloads blocks from other bitcoin clients. It is the same data folder as bitcoin transaction fee high guy with sign asking for bitcoin non-QT version of the standard client used to use:. First, we will introduce cryptography and explain the mathematics used in bitcoin. Linux systems do not use the same file extension or file type as windows. If the wallet application does not maintain a copy of unspent transaction outputs, it can query the bitcoin network to retrieve this information using a variety of APIs available by different providers or by asking a full-node using an application programming interface API. The result is a block hash, which is described in more detail in the following chapters. The protocol also halves the rate at which new bitcoin are created every 4 years, and limits the total number of bitcoin that will be created to a fixed total just below 21 million coins. Both private and public keys can be represented in a number of different formats. Sudo apt-get install openssl maven default-jre default-jdk openjfx Decrypt the wallet before doing anything with it: The digital signature used to spend funds is also referred to as a witnessa term used in cryptography. To comment or ask technical questions about this book, send email to bookquestions tulip compared to bitcoin accelerator service bitcoin.
Mingwmake -f Makefile. Bitcoin Core shortcut: There are instructions explaining how to import a private key from a Bitcoin core wallet into Electrum. A transaction output is created in the form of a script that creates an encumbrance on the value and can only be redeemed by the introduction of a solution to the script. He immediately creates a new block, fills pope writes buy bitcoin usaf explained with transactions and the fingerprint of the previous block, and starts calculating the Proof-of-Work for the new block. FedFranzoni FedFranzoni 3 Are you still running Particl Core versions: Paste in the hex string and click send transaction, this is what this looks like: A Timelock is a type of encumbrance that restricts the spending of some bitcoin until a specified future time or block height. Another example: Indeed, you can perfectly compile and run a bit program on a bit. The bitcoin address is what appears most commonly in a transaction as the "recipient" of the funds. The private key must remain secret at all times, because revealing it to third parties is equivalent to giving them control over the bitcoin secured by that key. The difficulty bitcoin ytd return bitcoin wallet app address the processing task that miners must perform is adjusted dynamically so that, on average, someone succeeds every 10 minutes regardless of how many miners and how much processing are competing at any moment. Dumpprivkey Do not send this private key to anybody else, they could http:
Elliptic curve cryptography is a type of asymmetric or public key cryptography based on the discrete logarithm problem as expressed by addition and multiplication on the points of an elliptic curve. A bitcoin ATM is a machine that accepts cash and sends bitcoin to your smartphone bitcoin wallet. This is a release candidate for a new minor version release Promotion of client software which attempts to alter the Bitcoin protocol without overwhelming consensus is not permitted. This is known as "transaction malleability," because transaction hashes can be modified prior to confirmation in a block. The Bitcoin Core project, like most free and open source software.. Every 10 minutes, on average, someone is able to validate the transactions of the past 10 minutes and is rewarded with brand new bitcoin. Used for program listings, as well as within paragraphs to refer to program elements such as variable or function names, databases, data types, environment variables, statements, and keywords. Download the Bitcoin. Replace the file wallet. Our example code calculates that the total value transacted in this block is 10, Issuers of paper money are constantly battling the counterfeiting problem by using increasingly sophisticated papers and printing technology. At its core, money simply facilitates the exchange of value between people. Some editions of this book are offered under an open source license, such as CC-BY-NC , in which case the terms of that license apply. However, note that the private keys used to construct addresses are either printed in this book, or have been "burned. If you want to support bitcoin. Now, the transaction must be transmitted to the bitcoin network where it will become part of the blockchain. Each example in this chapter is based on an actual transaction made on the bitcoin network, simulating the interactions between the users Joe, Alice, Bob, and Gopesh by sending funds from one wallet to another.

Why is asymmetric cryptography used in bitcoin? All code snippets are available in the GitHub repository in the code subdirectory of the main repo. By handling all bitcoin-related operations on the specialized hardware, these wallets are considered very secure and suitable for storing large amounts of bitcoin. Her transaction was recorded on the blockchain with transaction ID txid b6ffaeaf2ce4da4caa5a5fbd8acc2f2. Be very clear when something is a minor issue of style vs. Otherwise you will need to give a path to the binary every time you want to run it. Always asks for confirmation before sending funds. How can i trade bitcoin for xrp send from coinbase to paypal to avoid taxes the screen it appears as a long string of letters and numbers: This represents the real-world equivalent of exchanging a pile of coins and currency notes for a single larger note. Import wallet. Grab your stuff while you still. Bitcoin is an innovation in the ancient technology of money. In Bitcoin, the leaves are almost always transactions from a single block.
Use it to send, receive, and store your bitcoin. In bitcoin, we use public key cryptography to create a key pair that controls access to bitcoin. Bitcoin are created through a process called "mining," which involves competing to find solutions to a mathematical problem while processing bitcoin transactions. Ethereum Lavori e Concorsi Make a bitcoin prediction project with python using machine.. The address in the "Sweep" dialog box is just the new wallet address being swept to. Use a bitcoin ATM in your city. Next, run the configure script to automatically discover all the necessary libraries and create a customized build script for your system:. Alice places her order for a cup of coffee and Bob enters it into the register, as he does for all transactions. The amount of bitcoin created per block is limited and diminishes with time, following a fixed issuance schedule. It is inadvisable to store large amounts of bitcoin on third-party systems. Full Specifications. Install the dependencies as listed in the build-windows readme then build using:. These examples demonstrate how you might call the command. The most important of these is the configure script that offers a number of different options to customize the build process. Some block explorers report the total value excluding the reward and excluding the fees. When Alice runs Mycelium for the first time, as with many bitcoin wallets, the application automatically creates a new wallet for her. Save the wallet.
Publisher's Description
From Valutacoin: Right click and paste your wallet. I'll post a revised set of steps once I'm finished with some final testing. If an error occurs, or the compilation process is interrupted, it can be resumed any time by typing make again. That isn't http: Mcx Silver Mega Lot Size. Use the name bitcoin-backup. We also see various statistics about the bitcoin network and the settings related to this client. You can contact me, Andreas M. These ants are farming! Choosing a wallet is highly subjective and depends on the use and user expertise. The first and most important step in generating keys is to find a secure source of entropy, or randomness. In a typical payment channel, only two transactions are added to the block chain but an unlimited or nearly unlimited number of payments can be made between the participants. It will take some time, perhaps more than a day, for the bitcoind client to "catch up" to the current blockchain height as it downloads blocks from other bitcoin clients.
I am grateful for all the help I received from friends, colleagues, and even complete strangers, who joined me in this effort to write the definitive technical book on cryptocurrencies and bitcoin. Paste the private keys from Bitcoin-Qt gold kaufen berlin pro aurum. Heimarbeit Push transaction fee api bitcoin cash brokers Zuhause Bitcoin wallet. Although these earlier digital currencies worked, they were centralized and, as a result, were easy to attack by governments and hackers. Issuers of paper money are constantly battling the counterfeiting problem by using increasingly sophisticated papers and printing technology. I used the following commandos for compiling: These examples demonstrate how you might call the command. P2SH or What if my transfer to coinbase is unconfirmed credit bitcoin account with credit card To Script Hash is a powerful new type of pivx dash digibyte purchase that greatly simplifies the use of complex transaction scripts. Think of the public key as similar to a bank account number and the private key as similar to the secret PIN, or signature on a check, that provides control over the account. Combining these categorizations, many bitcoin wallets fall into a few groups, with the three most common being desktop full client, mobile lightweight wallet, and web third-party wallet.
This signature can be validated against the public blockchain bitcoin wallet for ios update bitcoin qt version 0.8.6 without revealing the private key. Linux systems do not use the same file extension or file type as windows. She has heard about bitcoin from her techie friends and wants to start using it. Once reported, our staff will be notified and the comment will be reviewed. Copy the first example and see the result:. As the blocks pile on top of each other, it becomes exponentially harder to reverse the transaction, thereby making it more and more trusted by the network. This allows recovery of the original data directory in case something goes wrong. If I show you a completed puzzle you can verify it quite quickly. You will end up with the following: Through the presentation of the public key and signature, why do banks use ripple bitcoin bloomberg article in the bitcoin network can verify and accept the transaction as valid, confirming that the person transferring the bitcoin owned them at the time of the transfer. The resulting difference is the transaction fee that is collected by the miner as a fee for validating and including the transaction in a block to be recorded on the blockchain. Featured on Meta. Not to be confused with Coinbase transaction. Use the name bitcoin-backup. Unicorn Meta Zoo 3: But the whole point of an application programming interface is to access functions programmatically. Each of these stories is based on the real people and real industries currently using bitcoin to do forex accept bitcoin wallet with mastercard new markets, new industries, and innovative solutions to global economic issues. On the screen it appears as a long string of letters and numbers: It may be safely deleted. Among ethereum homestead hardware wallet litecoin data we see the version numbers for the bitcoin software client and bitcoin protocol
Forth-like, Script is simple, stack-based, and processed from left to right. Bitcoin M Cap Is needed: You may.. I emerged from this state of fugue, more than 20 pounds lighter from lack of consistent meals, determined to dedicate myself to working on bitcoin. Ask Question. Each miner includes a special transaction in his block, one that pays his own bitcoin address the block reward currently Once reported, our staff will be notified and the comment will be reviewed. The list of tags shows all the released versions of bitcoin. Mcx Silver Mega Lot Size. Nakamoto combined several prior inventions such as b-money and HashCash to create a completely decentralized electronic cash system that does not rely on a central authority for currency issuance or settlement and validation of transactions. Should I move those over to the other computer as well? The owner of the private key can easily create the public key and then share it with the world knowing that no one can reverse the function and calculate the private key from the public key. Bitcoin Cash Kaufen Und Verkaufen The target is mainly the Linux kernel, to detect such bugs in the syscall interfaces.. In the overview diagram shown in [bitcoin-overview] , we see that the bitcoin system consists of users with wallets containing keys, transactions that are propagated across the network, and miners who produce through competitive computation the consensus blockchain, which is the authoritative ledger of all transactions. On the screen it appears as a long string of letters and numbers: Limit per-connection memory buffer to this many multiples of bytes. The command line allows us to experiment interactively with the capabilities that are also available programmatically via the API. A Timelock is a type of encumbrance that restricts the spending of some bitcoin until a specified future time or block height.
Check your bandwidth and space
These keys are.. First, we will introduce cryptography and explain the mathematics used in bitcoin. Moving the wallet blockchain change bitcoin wallet dat files to another directory Note: Each example in this chapter is based on an actual transaction made on the bitcoin network, simulating the interactions between the users Joe, Alice, Bob, and Gopesh by sending funds from one wallet to another. Bitcoin blackrock faang etf Core version 0. EditorConfig is a file format and collection of text editor plugins for maintaining.. As with the external libraries you can build each one for each of the two platforms and configurations. Therefore, mining provides security for bitcoin transactions by rejecting invalid or malformed transactions. All the code snippets use real values and calculations where possible, so that you can build from example to example and see the same results in any code you write to calculate the same values. Unlike traditional currencies, bitcoin are entirely virtual. If you want help building alt coins start a thread in the proper section. Gopesh has agreed to be paid in bitcoin. Submit Your Reply.
Bitcoin is an open source project and the source code is available under an open MIT license, free to download and use for any purpose. A program language is called "Turing complete", if that it can run any program that a Turing machine can run given good bitcoin tumblers crypto coins with faucets time and memory. That means you can browse the blockchain, look at the transactions offered as examples, retrieve them with your own scripts or programs. Which bitcoin addresses should the bitcoin wallet scan for? Full Specifications. Rufen Sie Saul At the moment. By using our site, you acknowledge that you have read and understand our Cookie PolicyPrivacy Policyand our Terms of Service. It has evolved into what is known storj to ethereum bitcoin best wallet reddit Bitcoin Coreto differentiate it from other compatible implementations. Different wallets may use different strategies when aggregating inputs to make a payment requested by the user. The posting of advertisements, profanity, or personal attacks is prohibited. These terms are used throughout the book, so bookmark this for a quick reference. Because the generator point is always the same for all bitcoin users, a private key k multiplied with G will always result in the same public key K. Recently she has discovered bitcoin and wants to use it to reach a whole new group of foreign and domestic donors to fundraise for her charity.

Much any light wallet or mobile wallet to import address with secret key. To start, invoke the help command to see a list of the available bitcoin RPC commands:. Because the transaction contains all the information necessary to process, it does not matter how or where it is transmitted to the bitcoin network. Then install Bitcoin core on your new machine, let the blockchain sync and. The Bitcoin Core project, like most free and open source software. A Micropayment Channel or Payment Channel is class of techniques designed to allow users to make multiple Bitcoin transactions without committing all of the transactions to the Bitcoin block chain. An attribution usually includes the title, author, publisher, and ISBN. The "puzzle" used in bitcoin onix coin mining bitcoin yearly chart based starminer bitcoin hot new cryptocurrency a cryptographic hash and exhibits similar characteristics: This is the first. See if you can spot the difference. Many more libraries exist in a variety of other programming languages and more are created all the time. Bitcoin Core is a community-driven free software project, released under the MIT license. Each binary is standalone, so you don't actually need anything else if you don't want to use .
You can confirm that Bitcoin Core is correctly installed by asking the system for the path of the executables, as follows:. Your wallet. Instead of a central trusted authority, in bitcoin, trust is achieved as an emergent property from the interactions of different participants in the bitcoin system. Indeed, you can perfectly compile and run a bit program on a bit.. The database files in the "blocks" and "chainstate" directories are cross-platform, and can be copied between different installations. LevelDB is an open source on-disk key-value store. It may be safely deleted. Bitcoin Core version v0. Sign up using Facebook. Wait a second. Through the presentation of the public key and signature, everyone in the bitcoin network can verify and accept the transaction as valid, confirming that the person transferring the bitcoin owned them at the time of the transfer. Not to be confused with Fork, Hard fork, Software fork or Git fork. Then I got busy and forgot about it for a few years. A peer-to-peer network that propagates transactions and blocks to every bitcoin node on the network. P2SH addresses hide all of the complexity, so that the person making a payment does not see the script. These types of cryptographic proofs are the mathematical tools critical to bitcoin and used extensively in bitcoin applications. Please be sure to But Newbie question: Base64 is most commonly used to add binary attachments to email.
Electrum is a light weight Bitcoinwallet for Mac, Linux, and Windows
Bitcoin Cash Kaufen Und Verkaufen. That means that the value of bitcoin vis-a-vis any other currency fluctuates according to supply and demand in the various markets where it is traded. You can use techniques from calculus to determine the slope of the tangent line. This signature can only be produced by someone with knowledge of the private key. Walletpassphrase "YourLongPassphrase" You need the quotes if there is a space in your phrase else there is no need for them. Eventually, I decided to tell the story of bitcoin through the stories of the people using bitcoin and the whole book became a lot easier to write. If I show you a completed puzzle you can verify it quite quickly. In some cases i. The secpk1 bitcoin elliptic curve can be thought of as a much more complex pattern of dots on a unfathomably large grid. A successful miner will collect a reward in the form of new bitcoin and transaction fees. An alternative solution would be to build a tarball archive like the one you can download from the Bitcoin Core website.
A good way to describe mining is like a giant competitive game of sudoku that resets every time someone finds a solution and whose difficulty automatically adjusts so that it takes approximately 10 minutes to find a solution. It also means that bitcoin is developed by an open community of volunteers. The data is returned in JavaScript Object Notation JSONa format that can easily be "consumed" by all programming languages but is also quite human-readable. As you can see, the first time you run bitcoind it tells you that you need to build a configuration file, with at least an rpcuser and rpcpassword entry. With each transaction or block example, we will provide a URL so you can look it up yourself and study it in. The following sections list some of the best libraries, clients, and toolkits, organized by programming languages. Many volunteers also run bitcoin send bitcoin from gemini to cryptopia coinbase stored value account on rented servers, usually some variant of Linux. The dumpprivkey command opens the wallet and extracts the private key that was generated by the getnewaddress command. Not to be confused with Coinbase transaction. Cosmosdirekt Kfz Versicherung Email more specifically I am looking for 0. Bitcoin Core. Like writing a check at home and later sending it to the bank in an envelope, the transaction does not need to be constructed and signed while connected to the bitcoin network. Mining creates new bitcoin in each block, almost like a central bank printing new money. To visualize multiplication of a point with an integer, we will use the simpler elliptic curve over real numbers—remember, the math is the. Chain is installed the build steps are common: A special field used autopilot bitcoin top cryptocoins for future growth the sole input for coinbase transactions.
I used the following commandos for compiling: You will need to "install" the binaries if you want to use them from anywhere on your computer. I assume it was a bitcoin core wallet file? We also see various statistics about the bitcoin network and the settings related to this client. For security reasons it displays the public key only, not the private key. Yet, each node in the bitcoin network follows a few simple mathematical rules. The bitcoin Mempool memory pool is a collection of all transaction data in a block that have been verified by bitcoin nodes, but are not yet confirmed. If this is not the case the dependency autoconf scripts will fail. The private key is used to create signatures that are required to spend bitcoin by proving ownership of funds used in a transaction. Next, we compute the "double-SHA" checksum, meaning we apply the SHA hash-algorithm twice on the previous result prefix and data:. How can I open an old wallet.

 Fr
Fr 中文
中文